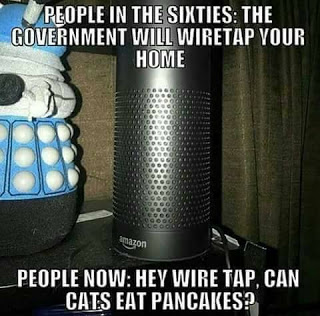
I saw this meme going around over the weekend.
I saw this meme going around over the weekend.
I laughed. Then I sighed.
Because it’s true.
Here’s where it stops being funny or just me being paranoid. Remember, there’s already a case in court determining whether or not the recordings generated by the “always on” feature can be used in a murder trial. This isn’t a new problem; we saw this with Samsung’s smart TV’s a few years ago.
But it wasn’t until this meme that I really realized how much we were all looking at the wrong thing.
Samsung’s defense was saying that information was only transmitted after the keyword was uttered… but that’s not the case across the board. Some of the other voice recognition folks store that data anyway, and not on your home system. For example, Google says that the data’s stored, but unless you’re logged in, it’s kept anonymously and not tied to your account. For services like Siri and Alexa and Google Now, simple commands might be processed on your device, but more complex answers are sent to a remote server that provides the response. And Cortana on Windows 10 seems to be still transmitting data – of some kind – even when disabled.
Which means that device is not only “always on”, but is potentially always transmitting. Sure, sure, there’s privacy policies. Hell, there’s groups like the newly-founded Voice Privacy Industry Group setting up “best practices” for companies.
That’s not the real problem.
It’s Not Just the Developers and Big Tech
The last round of Wikileaks dumps showed that the CIA not only knew about security holes that could let them listen in on secure communications. Oh, no, that’s not supervillain enough. The CIA knew about these security holes the day the devices and software got into the public’s hands – and usually before the company in question knew about the security problem. And they never did tell the tech companies what they’d found.
There’s a reason why “white-hat” hackers release info about security holes right away. They want problems can be solved so nobody can exploit them. Not so the CIA. They wanted to keep listening in, and didn’t think of the consequences.
As NYMag points out, this “means if the CIA knew about these exploits, you can bet other foreign and domestic actors did as well.”
Yes. That means Russia.
But “most” of those exploits were patched!
While Google and Apple are quick to reassure everyone that “most” of the CIA exploits are patched now, that doesn’t mean they were patched right away. Remember, the CIA knew about many of these before the tech companies.
And that’s when we’re talking about devices that get updated frequently. When you’ve got an older device – or one that’s not from the biggest names – you may not see security updates for a long time.
While we’re at it, don’t forget that Internet Of Things stuff – you know, like Alexa or the single press buy buttons from Amazon. Or your CCTV. Or your printer. Or your router. Or your modem?
Yes, Alexa (and Google Echo) get OTA updates. But the smaller devices? Heck no. Have you ever checked to see if there was an update for your router or modem? And if you did check, was there one? There have been real exploits that effected routers and modems in the last three years.
If you’re starting to worry, check out https://routersecurity.org for things to start checking and fixing.
But that’s still not the real problem.
Spies lie professionally, remember?
Let’s remember that – predating Trump – the NSA, FBI, and CIA have twisted the law (or outright lied) about spying on US citizens. They collected everything from records of most phone calls made in the USA, an unknown (but presumably large) number of e-mails, Facebook posts, and instant messages, “massive” amounts of internet data, and finally, lots of actual phone calls.
How’d they manage that? Turns out that with a global network like the internet, it’s not that uncommon for some of your traffic to go outside the country, which makes it legal for them to spy on you. And if they got a bunch of extra data too, well, that was just a big whoopsie. TERRORISM and all that.
Oh right, new decade. ISIL and all that.
Anyway, those didn’t really require any special exploits like the ones in the last leak. Those made it easier, but the spies didn’t really need it. Because there’s still one more giant problem.
The Biggest Problem
Top everything above with a big steaming pile of cooperation from your ISP. (AT&T gets named a lot, but they weren’t the only one that got outed – and that’s assuming that we know about all the ones participating.)
That’s the same ISP which is currently salivating. The GOP is giving them the opportunity to sell all your browsing and personal information without bothering to ask you first, so I’m pretty sure that your ISP is ready to roll over anytime they’re asked.
And probably some times before they’re asked.
Let’s be clear. This is your ISP – the company that has a near-monopoly in your area – keeping track of every site you visit, then both selling it and offering that information up to people spying on you.
Sure, maybe the NSA/CIA/FBI don’t have direct access to the servers at Google and Facebook and Amazon.
They don’t need to.
Putting Some Locks on the Doors
There are some ways you can keep some degree of privacy. Use a VPN (I use Private Internet Access). Make sure your router and modem are updated. Follow some of the settings in the links above. Encrypt your web communications using HTTPS Everywhere and limit tracking using Privacy Badger. Learn about encrypting your e-mail, texts, and calls. Make sure you use DNS servers like OpenDNS, Google’s, or DNS.watch (or your VPN’s if they have one – and they probably should.) And turn off as many of the “always listening” devices and apps as you can.
In some ways, this is like having a deadbolt on a standard door. A determined attacker (or spy) will get through, no matter what you do.
But that doesn’t mean we should go around leaving our doors – virtual or not – unlocked and wide open.
Got nothing to hide?
And please, for those about to say “I have nothing to hide”, go read the links at the bottom of the post – and if you still think that way, just send me a copy of every e-mail, text message, and letter you’ve ever sent. Add in the GPS data from your phone. Add in every web page that you’ve ever visited – even in “incognito mode”.
To paraphrase Cardinal Richelieu, “If one would give me six day’s full browser history of even the most honest person and I would find something in it to make them look awful.”
https://thenextweb.com/opinion/2016/02/11/i-have-nothing-to-hide-is-killing-the-privacy-argument/
https://www.openrightsgroup.org/blog/2015/responding-to-nothing-to-hide-nothing-to-fear